March 10, 2023
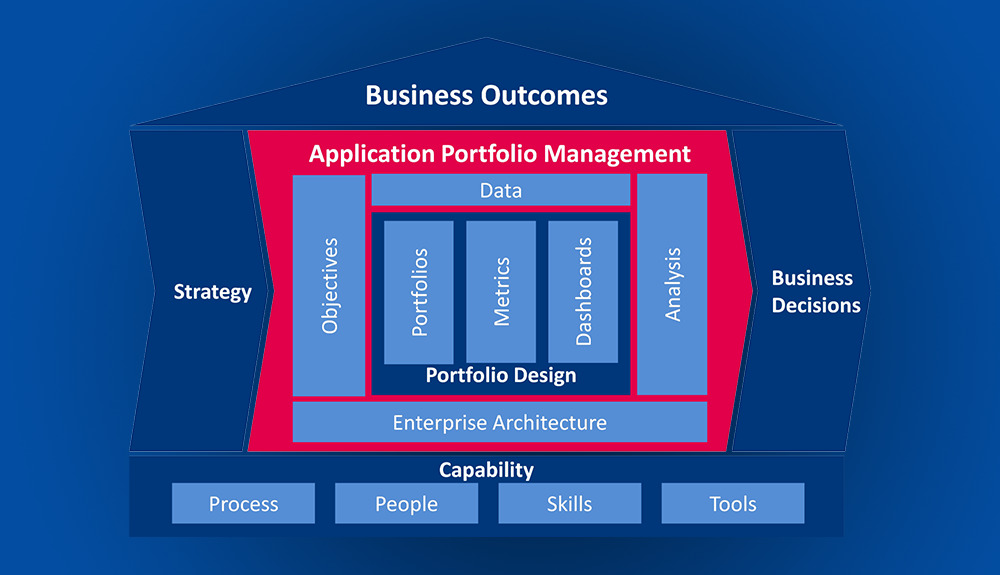
APM Software: What CIOs need for Application Rationalization with Actionable Insights

July 14, 2016
Enterprise Architecture: Key to Successful Business Transformations
- Adaptive Enterprise
- Application Portfolio Management
- BPM Business process management
- Business Architecture
- Business Capability
- Capability Based Planning
- Digital Transformation
- Enterprise Architecture
- Enterprise Architecture Software
- Enterprise Architecture Tools
- Enterprise Portfolio Management
- Security Architecture

March 3, 2015
Enterprise Portfolio Management: Getting Started
- Application Portfolio Management
- BPM Business process management
- Business Architecture
- Business Model Management
- Decision Model Management
- Enterprise Architecture
- Enterprise Architecture Software
- Enterprise Architecture Tools
- Enterprise Portfolio Management
- Lean Management
- Portfolio Management
- Project Portfolio Management
January 13, 2015
Business Transformation: Coordinating Enterprise Portfolio Management with Other Disciplines
- Application Portfolio Management
- Business Architecture
- Business Capability
- Business Model Management
- Capability Based Planning
- Enterprise Architecture
- Enterprise Architecture Software
- Enterprise Architecture Tools
- Enterprise Portfolio Management
- Governance Risk & Compliance
- Lean Management
- Portfolio Management
- Project Portfolio Management

December 14, 2014
Escaping the Jaws of the Project Monster
- Application Portfolio Management
- Business Architecture
- Business Capability
- Capability Based Planning
- Digital Transformation
- Enterprise Architecture
- Enterprise Architecture Software
- Enterprise Architecture Tools
- Enterprise Portfolio Management
- Governance Risk & Compliance
- Lean Management
- Portfolio Management
- Project Portfolio Management