Bizzdesign Unify: An AI-native platform for faster, better transformation decisions.
In today’s digital economy, it’s become increasingly important to architect an enterprise that can adapt and thrive in the face of constant change. Enterprise architecture is now more focused on meeting the demands of business transformation, with Enterprise Architects playing a key role in helping organizations become more efficient, flexible, and robust.
This document highlights the significance of a connected enterprise architecture that integrates business, IT, data, and risk perspectives to drive transformation initiatives.
It emphasizes the need for improved communication and collaboration between IT and the business, allowing Enterprise Architects to analyze the impacts of change and provide insights on how the organization should evolve to meet customer expectations, address competitive threats, and navigate market disruptions.
This shift in the practice also necessitates a new generation of enterprise architecture tools to support the evolving challenges facing Enterprise Architects.
The Evolution of the Enterprise Architecture Practice
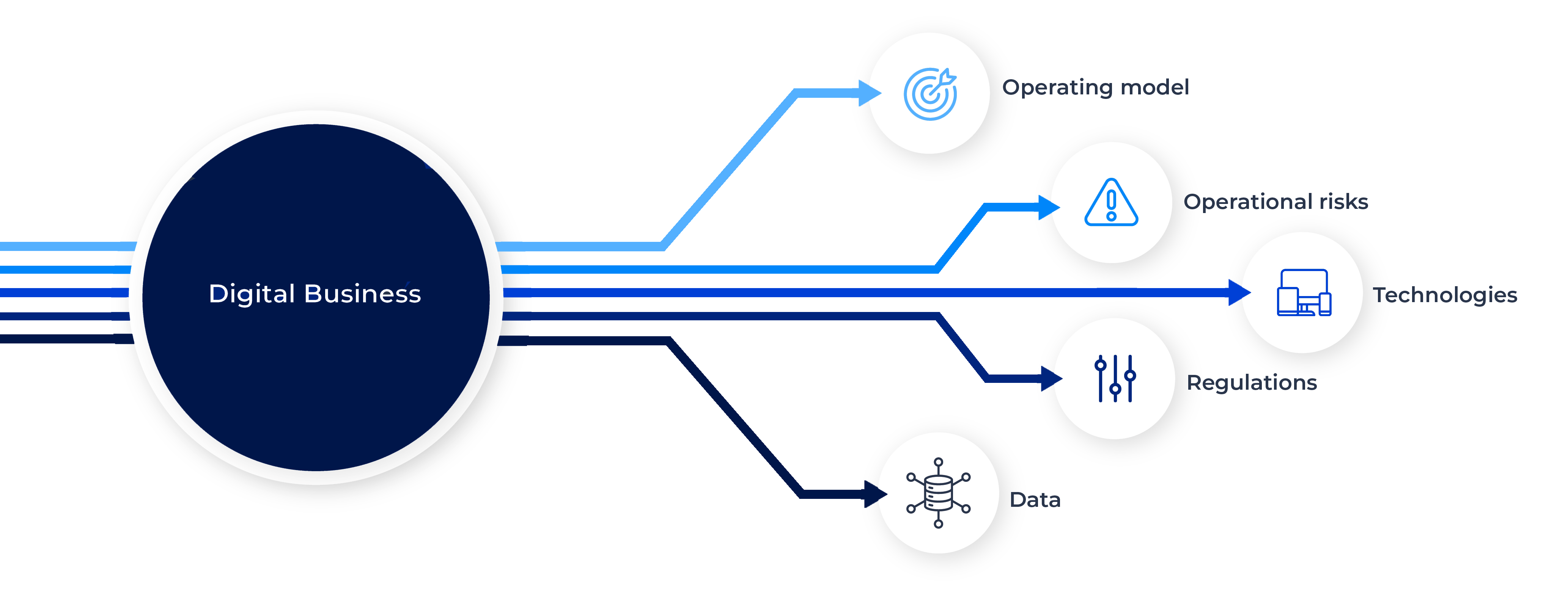
As business transformation accelerates, the value of enterprise architecture relies increasingly on analyzing the impacts of change to guide organizations in their transformations. This involves identifying not only the potential opportunities brought by using new digital technologies but also their impact on the operating model and possible risks.
From an IT-centric to a business-centric approach
Organizations have long used enterprise architecture (EA) to design and analyze their current and “to be” states. EA helps organizations understand how they operate across people, processes, and technology.
Enterprise architecture promises to act as the intermediary between Business and IT. But traditional EA, which takes a technology-centric approach, focusing on defining technologies, principles, and policies, stays in reactive mode and is far from supporting business goals and objectives.
Today, leading enterprise architecture practices are refocusing on the business because traditional IT-centric EA does not meet digital business demands.
The science of EA has been firmly established, and now, the discipline’s success lies in the art of managing and communicating it. A business-outcome-driven or business-centric enterprise architecture approach represents a shift in course, starting with the business rather than IT projects and initiatives.
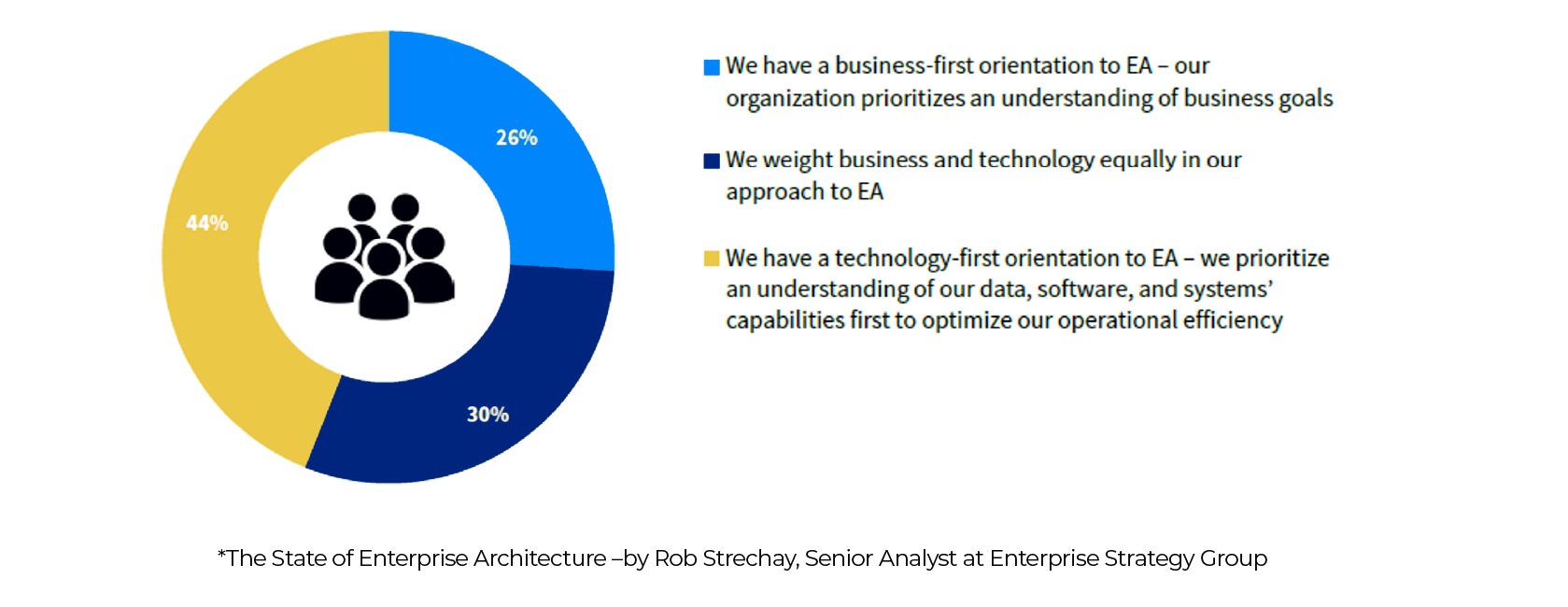
While 56% of organisations state that the shift toward a business-centric EA practice is well underway, 44% remain with a technology-first orientation.
Enterprise Architects as business enablers
In a business-centric approach, Enterprise Architects base their actions on understanding business strategies and outcomes and utilize a practical, proven approach to support business stakeholders.
By shifting from a purely IT focus to a more balanced approach encompassing business and IT, Enterprise Architects position themselves as business partners who effectively guide the leveraging of technology to support the business. They are problem solvers and proponents of business advancement. They share insights with leadership to help the organization gauge progress toward strategic goals and gather the necessary information to achieve business objectives. Whenever possible, they use automation tools to uncover data, allowing them to dedicate their time to providing enhanced recommendations to the business.
Enterprise Architects work for the CIO (Chief Information Officer), CTO (Chief Transformation Officer), or CDO (Chief Digital Officer), and assist them in streamlining the organization, making it more agile and resilient, thus enabling effective planning and adaptation to change.
Delivering Value with a Connected Enterprise Architecture Practice
What a “Connected EA” means
Successful transformation in a rapidly evolving digital business environment requires constant dialogue between teams unaccustomed to collaborating. Where IT, business, data, and risk perspectives are tightly intertwined, aligning stakeholders with common objectives takes time.
The key to unlocking organizations’ full transformative potential lies in connecting enterprise architecture with business processes, data governance, and risk management, enabling a comprehensive understanding of interconnectedness and interdependence.
“Learn how to see. Realize that everything connects to everything else.”
Leonardo da Vinci
The company’s holistic understanding of its operational ecosystem and the potential impact of changes across different organizational layers and domains is facilitated by a centralized data repository. This enables stakeholders to gain a comprehensive perspective and see the bigger picture.
The connected Enterprise Architecture approach is crucial for driving collaboration between IT and business stakeholders and empowering organizations to swiftly adapt to customer expectations, competitive challenges, and market disruptions.
By fostering collaboration and dismantling barriers between business stakeholders and the IT department, Enterprise Architects play a pivotal role in defining enterprise architecture and ensuring a clear understanding of business requirements and the rationale behind IT projects, using language that resonates with both groups.
Benefits of a connected enterprise architecture practice
Transformation does not work in silos, yet in many organizations, each department pursues its own goals without always understanding how they fit into the overall business objectives. This is not the result of a lack of goodwill but a lack of visibility into cross-functional projects.
Adopting a “Connected EA” approach brings multiple benefits to an organization. It helps each team leverage some of the work done by other departments and greatly improves their efficiency.

a cloud migration project
Connecting enterprise architecture to business processes to improve operational efficiency
As previously mentioned, one of the key trends impacting enterprise architects is the switch toward a more business-centric enterprise architecture.
By connecting applications to business processes and customer journeys, Enterprise Architects can better understand how the business operates. They can see how processes are delivered from an IT perspective, and when a process is changed or optimized, they can evaluate the impacts of this change on IT systems.
Business-centric EA helps architects understand which applications or IT systems to focus on to improve operational efficiency, customer experience, or product delivery.
On the other side, by seeing which applications support their business processes, business analysts better understand why some processes are not performing as expected or are failing to match customers’ expectations.
Connecting enterprise architecture to data to build an efficient data governance system
When executing transformation projects, one essential task for Enterprise Architects is to model new applications and systems and define how data flows between them. Most EA teams also include data architects focusing on how data is stored and structured in databases and by defining physical, logical, and conceptual models.
By connecting EA with Data Governance, Enterprise Architects get better visibility of the data quality used by applications.
They can also understand if data usage complies with applicable regulations, improving IT compliance.
The key benefit for the CDO and the data office is accelerating Data Governance initiatives by leveraging the work done by Data Architects to create data catalogs, business glossaries, and enterprise-wide conceptual data models. Enterprise architecture also helps all data stakeholders understand the context in which data is used and for which purpose.
Connecting enterprise architecture to risk, controls, and regulations to mitigate risks
One of the main tasks of enterprise architects is to understand application lifecycles to avoid reliance on outdated technologies. This helps organizations reduce IT risks such as disruptions or data breaches. Because of the acceleration of emerging technologies and the rise of shadow IT and cyber criminality, the number of regulations related to digital technologies has exploded.
To make sure IT leaders understand the scope of these regulations and the controls they must put in place to mitigate these IT risks, a new collaborative approach between IT, Risk, and Compliance leaders is required, an approach in which the role of Enterprise Architect is essential in identifying and assessing IT risks. At the same time, Risk and Compliance stakeholders apply the appropriate controls to minimize business impact.
This close collaboration is essential to architect a more resilient organization and ensure business continuity.
Adopting a Business-Outcome Driven Approach
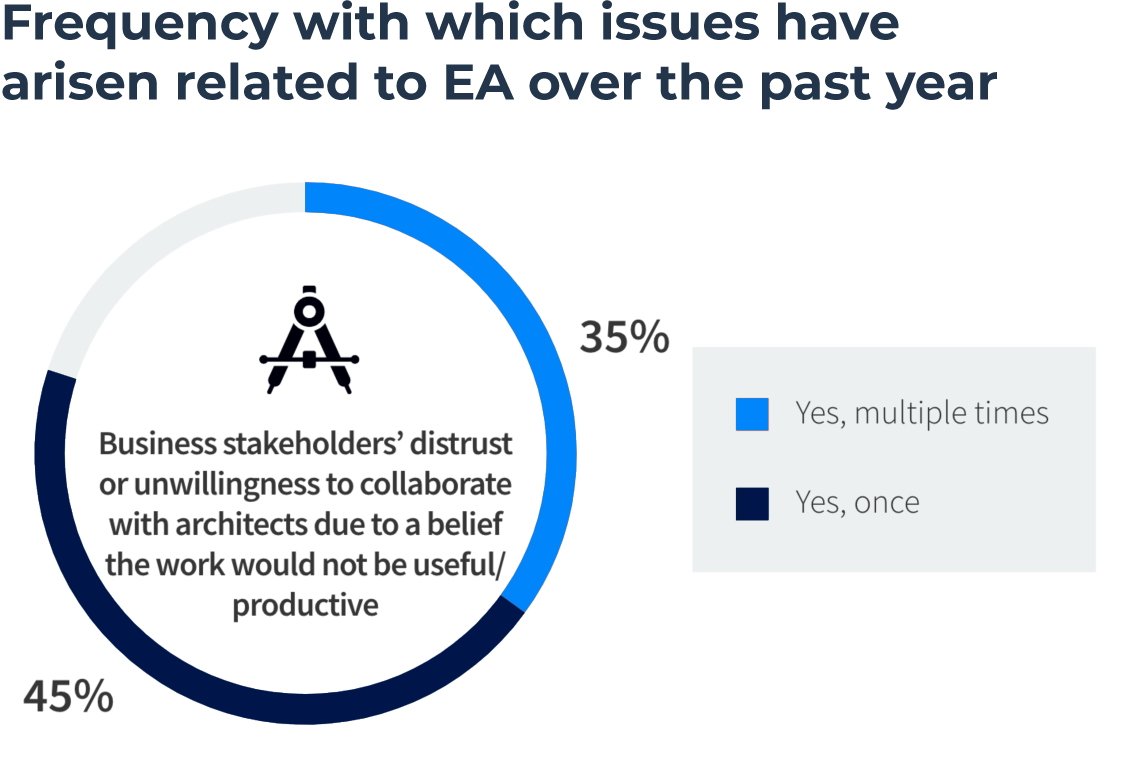
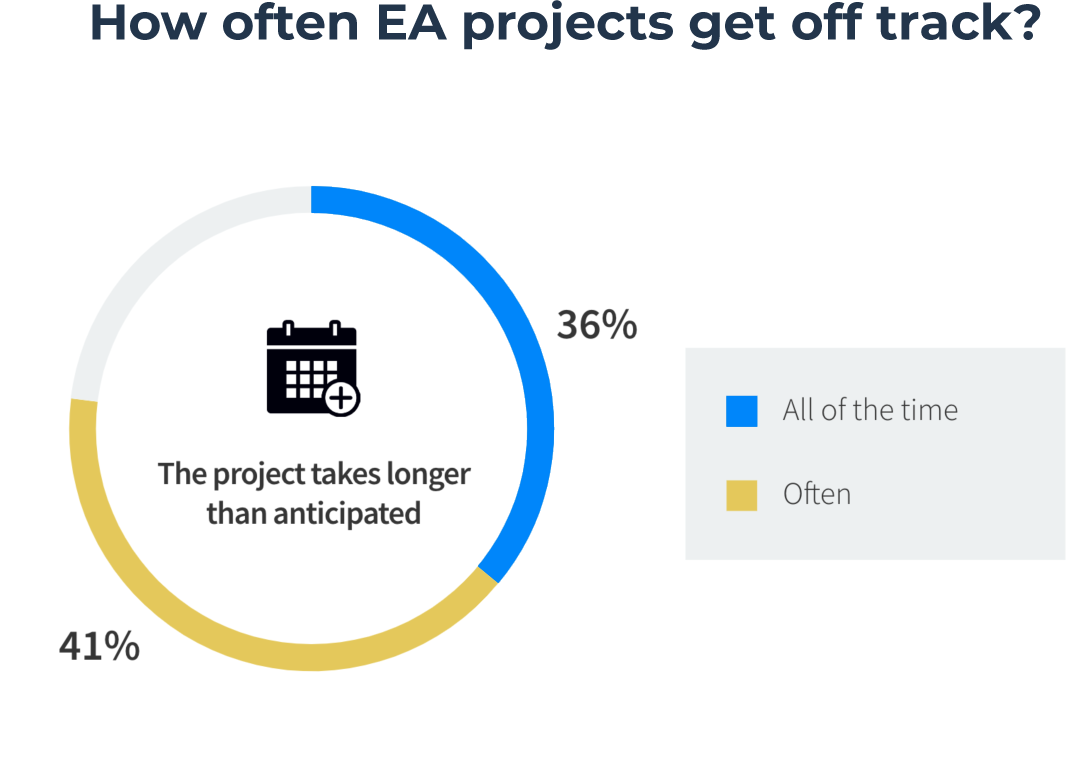
Eighty percent of organizations say they are having difficulties driven by business stakeholders’ distrust or unwillingness to collaborate with Architects due to a belief that the work would not be useful or productive. This challenge can make EA teams struggle for success, as shown by the 77% of organizations that report projects take longer than anticipated.
The typical challenge faced by Enterprise Architects is the difficulty of demonstrating value internally and the perception of inherent complexity. Therefore, Architects need to adopt a very pragmatic business-outcome driven approach based on a few simple principles, enabling intermediary quick wins while building on long term future success.
Demonstrate business achievements by quickly creating a solid Enterprise Architecture baseline
Architects are sometimes referred to as working in an ivory tower, because they are driven by documenting and planning everything, which represents considerable effort and may not provide the expected value to the business in a timely manner.
But creating a solid enterprise architecture baseline, by collecting just enough data, leveraging enterprise architecture tools, facilitating this inventory phase with automation, discovery, templates, and methodology features, enables not only the right deliverables for a project, but also ensures their consistency without losing time and focus on the results.
Grow the perceived value of enterprise architecture
If enterprise architecture’s end goal is to support business transformation and governance, the key to success is to apply a step-by-step approach and grow progressively. In other words, think big but start small.
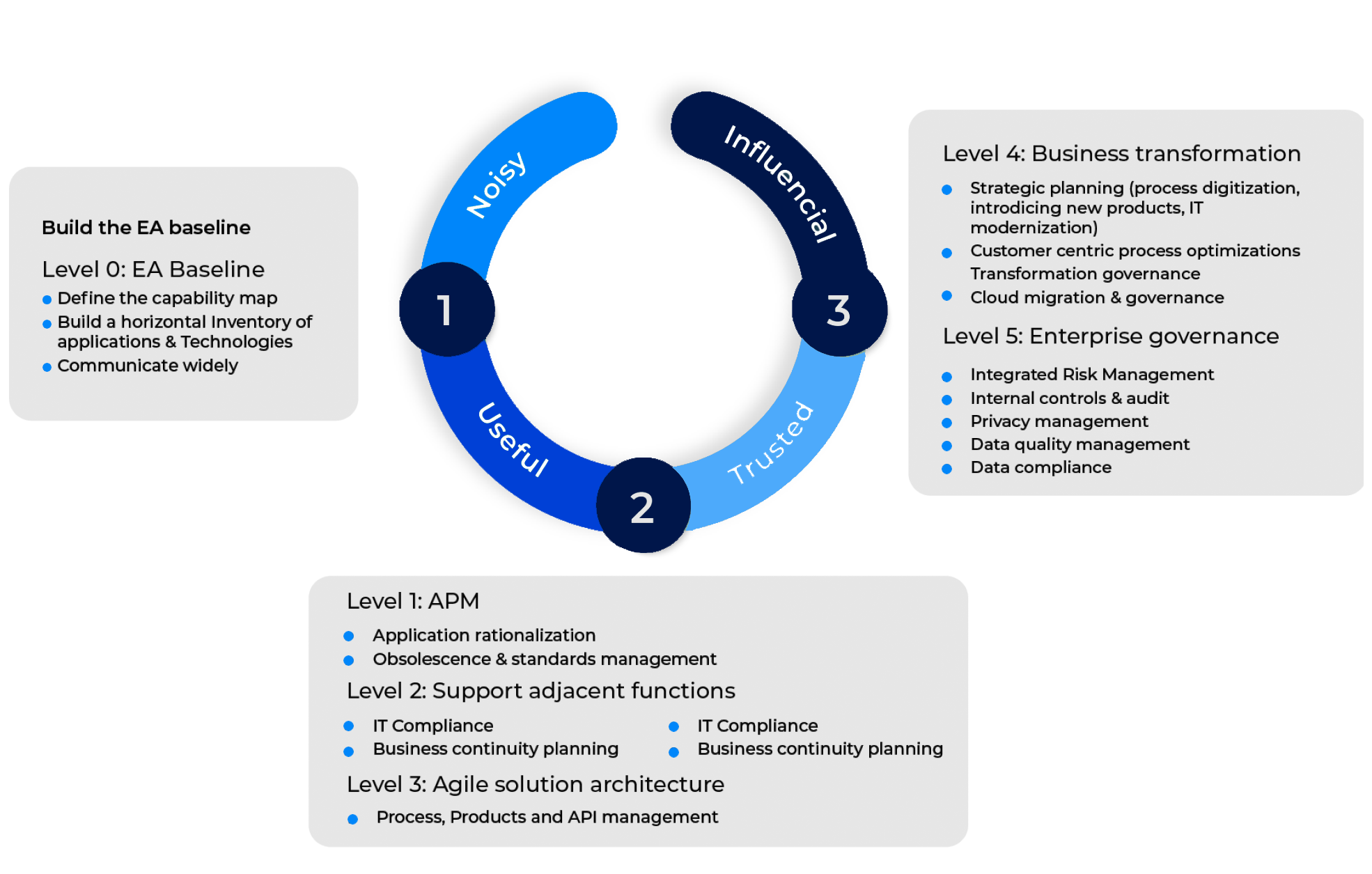
Bizzdesign has created a practical approach to empower architects to enhance the perceived value of their enterprise architecture practice. This approach aims to transition architects from the “Noisy” stage, characterized by a struggle for attention and perceived low business value, to the “Influential” stage, where architects play a pivotal role in shaping strategic decisions.
- Quickly getting from “Noisy to Useful” is key to demonstrate value, secure budget, and plan for broader use-cases. To become “Useful”, architects build the EA baseline, which minimally consists of creating a horizontal application and technology inventory, capability maps, and engaging in communication.
- Nevertheless, the full value of enterprise architecture is not reached at the “Useful” stage. Once you have established the EA baseline, start building a roadmap of use-cases, which will progressively grow the perceived value of the EA practice to “Trusted” and “Influential” positions.
Using a data-driven tool for a connected EA practice
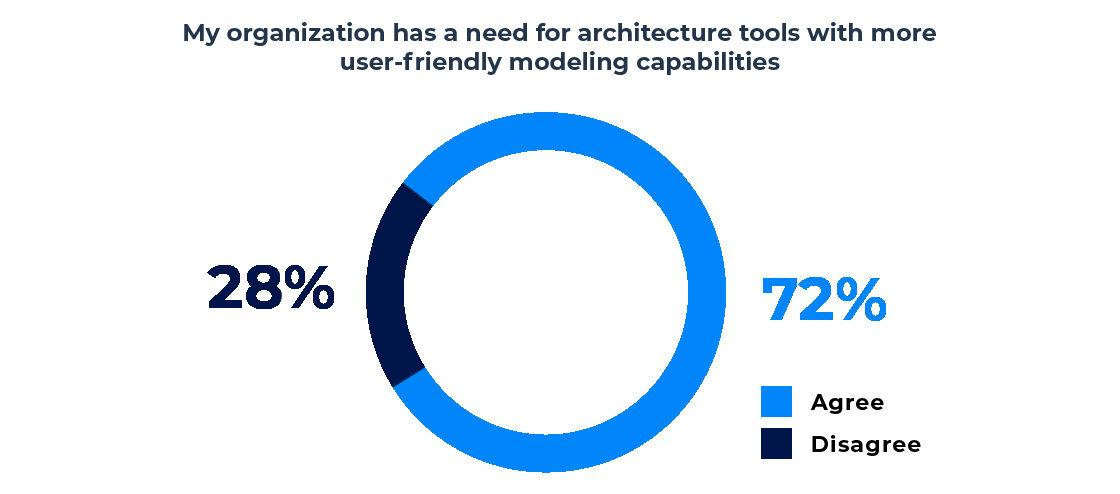
To implement a connected enterprise architecture practice, Enterprise Architects need a new generation of enterprise architecture tools that facilitate communication and alignment across the organization, accelerate routine tasks that take up Architects’ time, and provide data-driven insights to make decisions quickly and with confidence.
Only enterprise architecture tools sharing a single repository on a common platform with automated and intelligent features enable all stakeholders involved in transformation projects to share a common under-standing of the business purpose of these initiatives and collaborate to achieve common business goals.
Get a 360° view of the organization and improve collaboration with a single repository
One of the main pitfalls in transformation projects is that each department can pursue its goals without always connecting with the other departments and understanding how the whole should work together. Most of the time, this is due to a lack of visibility into cross-functional projects.
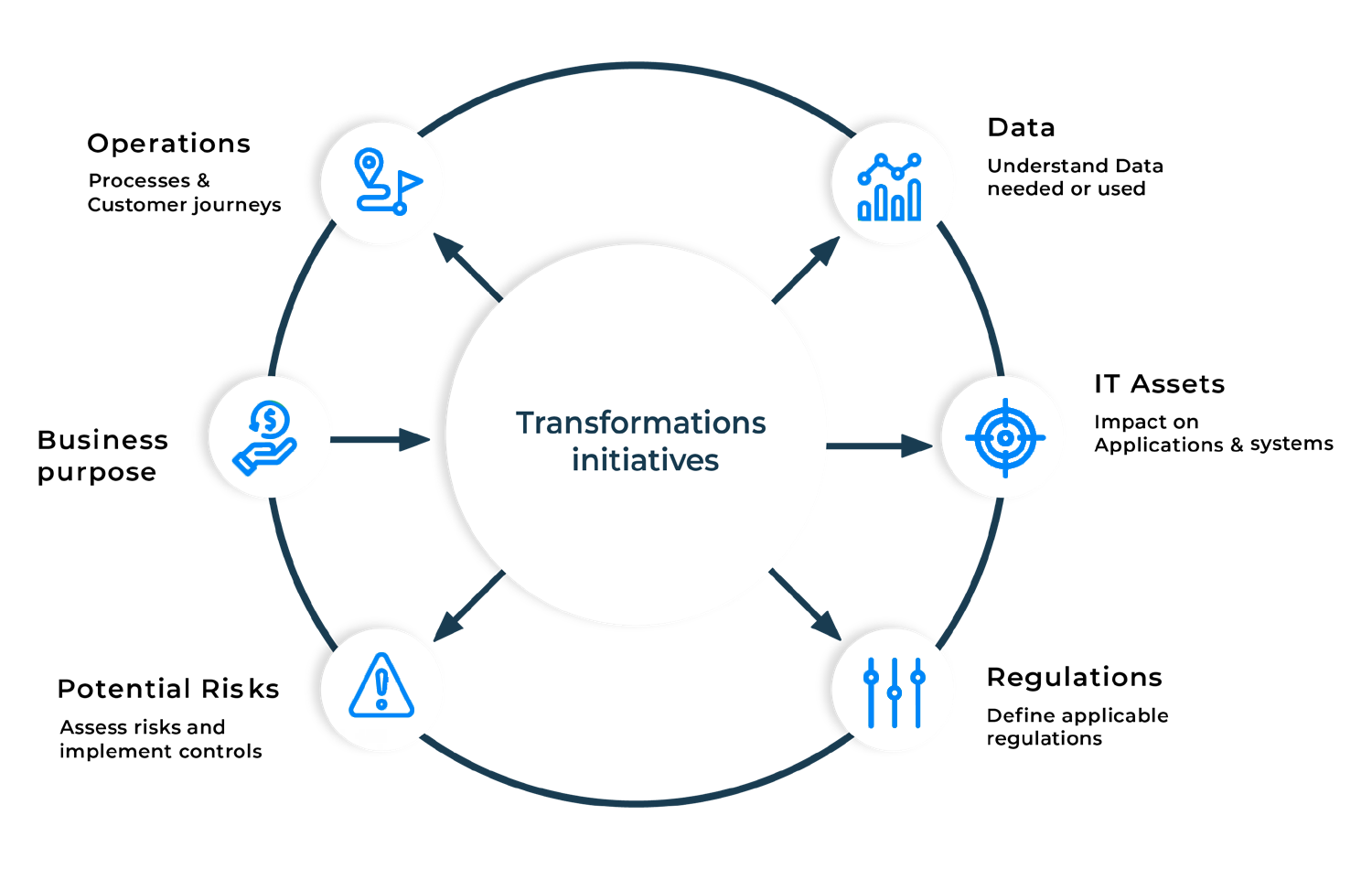
A single repository enables IT and Business to share a 360° view of how transformation initiatives impact operations and IT systems. By connecting strategy, business, IT, data, and risk perspectives on the same platform, all stakeholders see and understand interdependencies between these domains. This single source of truth simplifies communication, fosters collaboration, and reduces silos between departments.
In addition, organizations can better understand what data is needed or used to support projects and ensure that the new operations will be performed by regulations and with a clear visibility of the potential business and IT risks.
Save time and accelerate project delivery with automation
According to a recent study on the state of enterprise architecture from ESG, over 70% of Enterprise Architects state that EA projects often take longer than expected, with 36% saying that this happens all the time.
A next-gen enterprise architecture tool automates tasks that slow down Enterprise Architects. Use a solution with automatic IT discovery tools and Excel imports to speed up inventory. Enterprise Architects also need simple but powerful modeling capabilities to support many use cases. Therefore, Architecture templates and automatic diagramming save time for IT Architects designing new applications or systems.
Provide data-driven insights with smart recommendations
Leveraging the data contained in the enterprise architecture repository to make the right decisions may also become overwhelming when Enterprise Architects must balance multiple perspectives, such as risk, cost, business criticality, technical efficiency, etc.
A next-generation enterprise architecture tool proposes a smart recommendations engine based on algorithms that leverage data from the repository to provide smart data insights. Such capability helps Enterprise Architects quickly see which applications can be tolerated, invested in, modernized, or eliminated—following Gartner’s TIME optimization model—to best rationalize IT assets or to define the best cloud migration strategy by proposing which applications should be migrated, rehosted, or rebuilt.
The recommendations can be validated or rejected, and the decision is recorded to keep track of who made it and why. This facilitates the IT governance process, which becomes a great way to share decisions among all stakeholders.
Conclusion: Building an influential EA practice towards business transformation
The rapid shift to a digital economy necessitates robust, adaptable, and future-proof enterprise architectures. This white paper underscores the evolution of enterprise architecture from an IT-centric to a business-centric approach, positioning Enterprise Architects as key enablers of business transformation.
By aligning enterprise architecture with business, IT, data, and risk perspectives, organizations can drive transformation initiatives more effectively.
Enterprise Architecture is pivotal in navigating business transformations by breaking down silos, fostering collaboration, and aligning technology with business strategies. By leveraging advanced enterprise architecture tools and methodologies, IT leaders can drive significant value, demonstrating EA’s critical role in achieving strategic business objectives and maintaining a competitive edge.
Table of contents
More on this



