Bizzdesign Unify: An AI-native platform for faster, better transformation decisions.
April 30, 2026 - Brian George - Application and Technology Management

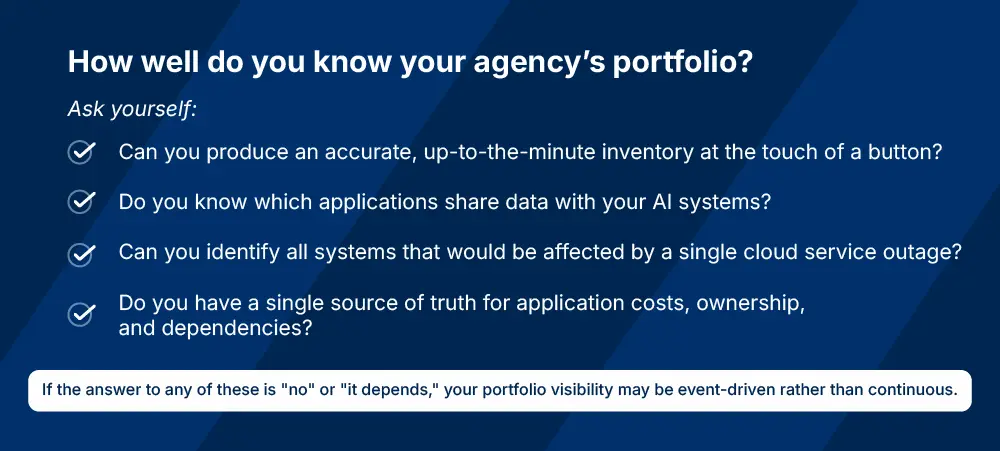
How many systems or applications does your agency operate? How many are redundant? Which ones are unused? Which ones touch Personally Identifiable Information (PII)? If you can't answer those questions in real time, you're not alone; but you're also not prepared for what's coming.
Government departments and agencies are under pressure to modernize faster while controlling costs, strengthening cybersecurity, and governing emerging technologies such as artificial intelligence (AI).
For government IT leaders, these expectations translate into overlapping demands: annual portfolio reviews required under the Federal Information Technology Acquisition Reform Act (FITARA), ongoing modernization and cloud transformation, tightening cybersecurity oversight, and fast-rising expectations for AI governance and transparency.
Translating those mandates into operational outcomes requires a reliable and continuously updated view of the application portfolio so leaders understand which systems exist, what they cost, which mission services they support, and how they interconnect.
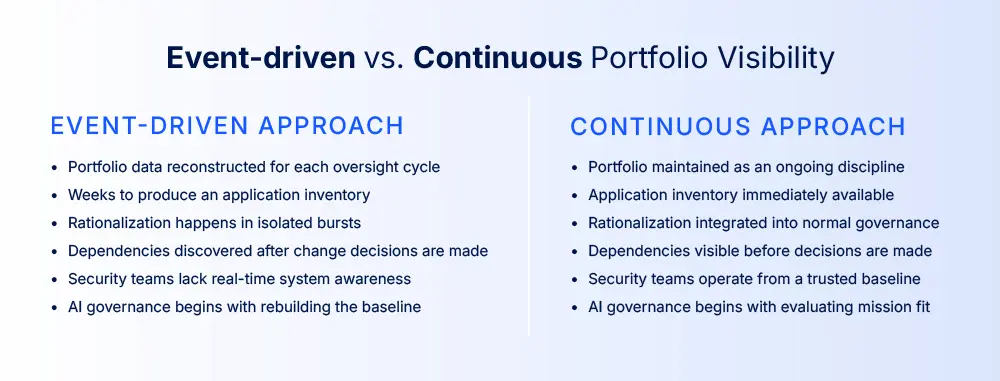
In practice, however, that visibility is often assembled piecemeal or in response to an impending event. Application inventories and portfolio information are frequently reconstructed only when oversight cycles require it, for example during audit preparation, budget submissions, or major modernization initiatives. Even the governance processes intended to maintain portfolio visibility can prove difficult to sustain. The Government Accountability Office's November 2024 (GAO) assessment, for example, found that many agencies have not consistently met FITARA's statutory requirement to conduct even annual IT portfolio reviews.
As modernization programs accelerate, cybersecurity obligations tighten, and agencies expand the use of AI systems, these fragmented and episodic portfolio practices create growing operational constraints. Leaders are expected to make modernization, cost, and risk decisions across environments they cannot always see clearly. Without a complete and up-to-date view of the application portfolio, oversight across cost, security, and technology initiatives becomes significantly difficult.
Why Maintaining Application Portfolio Visibility Is Operationally Difficult in Government
Government application portfolios are inherently difficult to map and maintain because they evolve across many systems, programs, and organizational boundaries. These environments rarely exist as neatly maintained inventories. Over time they evolve through successive modernization programs, policy changes, and organizational restructuring, creating technology landscapes that accumulate hidden complexity and technical debt.
Because these environments evolve across multiple systems and organizational units, portfolio data rarely resides in a single authoritative source. Financial records, procurement systems, configuration management databases (CMDBs), enterprise architecture repositories, and program offices each maintain fragments.
Agencies therefore assemble a complete portfolio view by aggregating information across these systems, often through manual reconciliation or spreadsheet-based reporting. While this approach can produce an accurate snapshot for a specific oversight cycle, it doesn't create a continuously reliable baseline. In practice, portfolio visibility is repeatedly reconstructed to meet audit, reporting, and leadership requirements, reducing efficiency and delaying decision-making.
Application Portfolio Management (APM) addresses this challenge. APM is an ongoing discipline that helps an organization maintain a continuously updated and authoritative view of its application landscape, including which systems exist, what they cost, what business capabilities they support, how they interconnect, and what risk they carry. By establishing portfolio visibility as a continuous practice rather than a periodic exercise, APM enables agencies to respond quickly to oversight requirements, modernization opportunities, and emerging risks without reconstructing the baseline each time.
That continuous visibility becomes the foundation for more confident decisions across three increasingly demanding areas of government IT oversight: cost control, cybersecurity, and AI governance.
Controlling IT Costs Starts with Application Portfolio Visibility
Cost control is often the most visible pressure point, and the first place where ad hoc portfolio practices create operational friction. Federal agencies spend more than $100 billion annually on IT and cyber-related investments, with approximately 80% devoted to operating and maintaining existing systems rather than modernization. In such an environment, even small inefficiencies across the application landscape can translate into significant long-term spending waste.
One of the most effective mechanisms for addressing this challenge is application rationalization, a core discipline within Application Portfolio Management (APM). By systematically evaluating applications against the business capabilities they support and relevant KPIs, rationalization enables agencies to identify and eliminate redundant, unused and outdated systems to reduce costs, and redirect funding toward higher-value modernization initiatives.
Recognizing the importance of this discipline, the Federal CIO Council published the Application Rationalization Playbook, which provides a structured approach for agencies to inventory, assess, and optimize their application portfolios. The Playbook emphasizes repeatable portfolio assessments, governance processes, and cross-agency transparency as the foundation for sustained cost control and modernization planning.
When executed effectively, rationalization can deliver meaningful financial benefits. Retiring redundant or underutilized applications reduces licensing expenses, simplifies the IT landscape, and frees budget for strategic investments. The GAO 2025 Annual Report, for example, estimates that improved IT portfolio management could save more than $100 million by reducing duplicative IT investments and halting or terminating investments when appropriate.
Maintaining continuous portfolio visibility through APM enables application rationalization as an ongoing discipline. This removes the need to reconstruct portfolio data during oversight cycles and gives leaders the ability to assess application costs continuously, model the financial impact of decisions before committing budget, and identify consolidation opportunities earlier in the planning process.
This shift allows agencies to move from one-off cost-cutting exercises toward sustained portfolio optimization where rationalization becomes part of normal portfolio governance.
Cybersecurity Oversight Depends on Accurate Application Inventories
Continuous portfolio visibility matters beyond cost control. As cybersecurity oversight continues to tighten across the federal enterprise, understanding the full application landscape becomes equally critical for managing risk.
Federal cybersecurity frameworks increasingly emphasize continuous monitoring and system visibility as prerequisites for effective risk management. Under the Federal Information Security Modernization Act (FISMA), agencies are required to maintain inventories of their information systems and continuously monitor them for security risks. National Institute of Standards and Technology (NIST) guidance further defines information security continuous monitoring as maintaining ongoing awareness of vulnerabilities and threats to support risk-based security decisions.
Achieving that objective requires security teams to maintain a clear understanding of which applications exist, how they connect to shared data environments, which external services they depend on, and which systems may introduce operational or security risk. Maintaining that visibility becomes significantly more complex as agencies migrate workloads to cloud platforms, integrate third-party services, and operate hybrid technology environments spanning on-premise infrastructure and multiple cloud providers.
When application portfolio data is fragmented across multiple systems and updated only intermittently, security teams lack a current, consistent view of the environment they are responsible for protecting. Incomplete inventories obscure dependencies between applications, make it harder to identify unsupported or vulnerable assets, and complicate efforts to prioritize remediation activities across the enterprise.
Continuous portfolio visibility ensures that application inventories, dependencies, and ownership information remain synchronized across systems and accessible for governance decisions. Instead of reconstructing the application landscape during periodic security reviews, agencies can maintain a continuously updated view of the systems operating across their environment.
This visibility allows security teams to identify emerging risks earlier, understand how vulnerabilities may propagate across interconnected systems, and prioritize remediation efforts based on a comprehensive view of the enterprise application landscape.
AI Governance Demands Continuous Portfolio Visibility
The continuous visibility required for cybersecurity oversight becomes even more critical as agencies scale AI adoption. Federal AI use has expanded rapidly, with approximately 3,000 AI use cases and systems reported as of early 2026. OMB's updated guidance (M-25-21) directs agencies to accelerate responsible AI adoption while strengthening governance, risk management, and transparency. Agencies are required to inventory AI use cases, designate Chief AI Officers, and conduct ongoing reviews of AI systems. Public AI inventories now list hundreds of use cases across all stages of maturity ranging from pre-deployment and pilot to fully deployed or retired.
GAO has reported that agencies face significant challenges scaling advanced technologies, including generative AI, due to governance, data quality, and infrastructure constraints. Scaling these technologies responsibly requires architectural clarity across the enterprise because AI systems don't operate independently. They draw from existing applications, integrate with legacy platforms, depend on shared data stores, and introduce new risk considerations. Many also depend on underlying cloud infrastructure decisions and third-party services.
The value AI can deliver therefore depends heavily on the architectural context in which it operates. Understanding how applications, infrastructure, and data interact across the organization is essential to evaluating where AI can deliver mission value and where it may introduce operational, financial, or security risks. Those same interdependencies must also be understood for agencies to inventory AI systems, assess risk, and maintain the oversight expected under OMB's responsible AI adoption.
When application portfolio information must be reconstructed for each oversight cycle, enterprise architecture teams spend capacity revalidating inventories and reconciling dependencies before AI initiatives can even be evaluated within the broader technology landscape.
In other words, when portfolio visibility is ad hoc, architecture teams have to rebuild the enterprise context needed to evaluate AI initiatives before governance decisions can begin. Each reset consumes capacity that could otherwise be spent assessing where AI can deliver measurable mission impact, identify unintended cost and security exposure, align new initiatives with existing modernization priorities, and prevent fragmented investments across the organization
AI initiatives may progress within individual programs, but without a continuously maintained enterprise baseline, scaling them responsibly across the organization becomes materially more difficult.
What Continuous Application Portfolio Management Changes
For agencies that succeed in establishing continuous portfolio visibility, the operational impact can be significant.
Minnesota IT Services (MNIT), which provides centralized IT services for 38 state agencies, faced many of the challenges common across government: fragmented application inventories, redundant contracts, and limited transparency across a highly federated technology environment. Instead of treating portfolio visibility as a periodic reporting exercise, MNIT re-established application portfolio management as an ongoing discipline and made a centralized platform the authoritative system of record for its application landscape.
Within 18 months, adoption expanded from just 25 early users to more than 200 active participants across agencies. Governance policies reinforced the practice operationally: new infrastructure could not be provisioned unless the associated applications were registered in the portfolio baseline. This shift transformed fragmented application lists into a continuously maintained enterprise view of systems, technologies, and vendor relationships.
With that visibility in place, MNIT was able to identify redundant contracts across agencies, support more informed cloud and modernization planning, and provide executive leadership with enterprise-wide dashboards showing the state's IT environment. Portfolio visibility moved from a reporting exercise to an operational foundation for governance and decision-making.
“That's when you can go to decision-makers and make the case for significant funding, because you can show exactly what you have today and the direction you need to move in.” — Chris Bucksa, MNIT Continuity of Operations Lead
Many agencies are addressing this challenge by adopting purpose-built application portfolio management platforms that maintain a continuously synchronized portfolio baseline. Some of the platforms are FedRAMP-authorized for SaaS deployment for use by the US federal government. Platforms such as Bizzdesign Alfabet, an application portfolio management platform aligned with the CIO Council Application Rationalization Playbook, enable agencies to maintain authoritative application inventories, integrate portfolio data across systems, and evaluate modernization or AI initiatives against a continuously updated enterprise architecture context.
For agencies evaluating how to make that shift from event-driven portfolio reviews to continuous management, our Buyer's Guide to Application Rationalization Platforms for US Government Supporting the CIO Council Playbook shows how to operationalize the Playbook in practice with purpose-built platforms to begin building continuous portfolio visibility using application rationalization as the catalyst. The guide outlines the capabilities required to support each step of the Playbook, integration requirements for continuous portfolio data synchronization, governance structures that sustain rationalization beyond initial assessments, and ROI frameworks that quantify cost avoidance and capacity protection.
As government technology environments grow more complex and oversight expectations continue to expand, maintaining a continuously reliable view of the application portfolio is no longer simply an architectural best practice. It is becoming a foundational capability for governing cost, cybersecurity risk, and emerging technologies across the enterprise.

FAQs
What is Application Portfolio Management (APM)?
Application Portfolio Management (APM) is the practice of governing the applications used in an organization. It is an essential strategic planning capability of an IT organization, ensuring that investments in the application landscape are in line with business strategy and that investments are made in a way that minimizes cost and risk, while at the same time delivering the required functionality and flexibility to fulfil business goals.
APM makes visible how applications map to business capabilities, where functional duplication drives unnecessary cost, which technical debt poses the greatest risk, and which dependencies must be managed before change can proceed safely. This visibility allows leaders to prioritize rationalization and modernization based on portfolio-wide impact rather than isolated business cases, helps teams identify consolidation opportunities during mergers or divestitures, and provides the foundation for cloud migration strategies that balance ROI against risk. When application strategy connects to the wider ecosystem of business capabilities, processes, data, and technology, organizations can plan, design, and govern change with confidence.
What is application rationalization and why is it important for government agencies?
Application rationalization is the structured, repeatable process of evaluating an application portfolio to determine whether individual applications should be retained, modernized, consolidated, migrated, or retired based on business value, technical health, cost, risk, and dependencies.
Without structured rationalization, agencies often struggle to identify which systems support mission services, where duplicative capabilities exist, how costs are distributed across the portfolio, and where operational or cybersecurity risks accumulate. For public sector agencies, application rationalization provides visibility into mission support, functional duplication, cost distribution, and risk exposure. This visibility enables agencies to control IT operating costs, reduce cybersecurity exposure, eliminate redundant systems, and ensure technology investments remain aligned to mission priorities. When executed as a continuous discipline rather than a periodic cleanup exercise, rationalization becomes a strategic capability that supports faster modernization, stronger governance, and more defensible investment decisions.
What is the difference between application rationalization and application portfolio management (APM)?
Application rationalization is the structured process of evaluating applications to determine whether they should be retained, modernized, consolidated, migrated, or retired. Application Portfolio Management (APM) is the broader discipline of governing applications across their full lifecycle from acquisition through retirement.
Rationalization is a foundational activity within APM, but APM extends beyond periodic assessments to include continuous portfolio visibility, lifecycle governance, investment planning, and alignment with enterprise architecture. When agencies establish authoritative application data and standardized evaluation processes through rationalization, the same foundation supports ongoing APM-adjacent disciplines such as technology portfolio management, strategic portfolio management, and AI governance. Rationalization provides the baseline; APM sustains it as an operational discipline. With purpose-built APM capabilities, Bizzdesign Alfabet enables agencies to initiate rationalization and then extend the same repository and governance workflows into continuous strategic portfolio management.
How does application portfolio management (APM) support government modernization initiatives?
Federal agencies allocate approximately 80% of their IT budgets to operating and maintaining existing systems, leaving limited funding for modernization. Application Portfolio Management (APM) addresses this constraint by providing the portfolio visibility needed to identify consolidation opportunities, retire redundant systems, and redirect funding toward higher-value initiatives.
When agencies maintain a continuously updated view of their application landscape through APM, they can evaluate modernization opportunities against a complete understanding of dependencies, costs, and mission alignment. This allows leaders to model the financial impact of portfolio decisions before committing budget, assess cloud migration candidates based on technical health and business value, and prioritize modernization investments that deliver measurable mission outcomes. The Federal CIO Council's Application Rationalization Playbook emphasizes repeatable portfolio assessments and governance processes as the foundation for sustained modernization planning. Bizzdesign Alfabet operationalizes this approach by connecting applications to business capabilities, costs, and technical dependencies within a centralized repository, enabling agencies to sustain modernization as a governed discipline rather than an episodic initiative.
Why do government agencies need continuous application portfolio visibility?
Government agencies face converging oversight demands: FITARA portfolio reviews, FISMA cybersecurity compliance, OMB AI governance requirements, and ongoing modernization and cost control expectations. Meeting these mandates requires a reliable, continuously updated view of the application portfolio, not one that's reconstructed for each oversight cycle.
Without continuous visibility, agencies risk falling behind on statutory requirements. The Government Accountability Office's November 2024 assessment found that many agencies have not consistently met FITARA's requirement to conduct annual IT portfolio reviews. When portfolio visibility is ad hoc or event-driven, agencies spend time revalidating inventories and reconciling dependencies before governance decisions can begin. Continuous visibility allows agencies to respond to oversight requirements, assess modernization opportunities, and evaluate emerging risks without rebuilding the baseline each time.
How does application portfolio management (APM) support cybersecurity oversight and FISMA compliance?
FISMA requires agencies to maintain inventories of information systems and continuously monitor them for security risks. Application Portfolio Management (APM) provides the continuous portfolio visibility needed to meet this requirement by maintaining up-to-date application inventories, ownership information, and dependency maps.
Without continuous visibility, security teams risk operating without awareness of the full system landscape they're responsible for protecting, making it harder to identify unsupported or vulnerable assets and complicating efforts to prioritize remediation activities across the enterprise. Continuous APM visibility allows security teams to identify vulnerable or unsupported systems faster, understand how security risks may propagate across interconnected applications, and prioritize remediation based on a complete view of the enterprise landscape.
Why does AI governance require application portfolio visibility?
AI systems don't operate in isolation. They depend on existing applications for data inputs, integrate with legacy platforms, rely on shared infrastructure, and introduce new dependencies across the enterprise. To govern AI responsibly and meet OMB M-25-21 requirements for AI inventories and ongoing reviews, agencies need to understand how AI systems interact with the broader technology landscape. With approximately 3,000 AI use cases and systems reported across federal agencies as of early 2026, this architectural clarity becomes critical to scaling AI adoption responsibly.
Without continuous portfolio visibility, agencies risk delaying governance decisions and making it materially more difficult to scale AI adoption responsibly. Each time agencies must reconstruct the architectural context needed to evaluate AI systems, enterprise architecture teams spend capacity revalidating inventories and reconciling dependencies, consuming capacity that could otherwise be spent assessing where AI can deliver measurable mission impact. Application Portfolio Management (APM) provides the foundation that makes AI inventorying faster, more accurate, and aligned with enterprise modernization priorities.
How does application portfolio management (APM) help manage risks from generative AI adoption?
As federal AI adoption accelerates, with approximately 3,000 AI use cases reported as of early 2026, agencies face growing pressure to scale AI responsibly while managing operational, financial, and security risks. Generative AI systems introduce unique governance challenges because they depend on underlying application architectures, integrate with legacy platforms, consume data from multiple sources, and often rely on third-party cloud services.
Without continuous portfolio visibility, agencies risk deploying AI systems without fully understanding their dependencies, data lineage, or potential security exposure. Application Portfolio Management (APM) provides the architectural clarity needed to evaluate where generative AI can deliver mission value and where it may introduce unintended risks. By maintaining an authoritative view of AI usage in applications, data flows, and infrastructure dependencies, agencies can assess AI initiatives within the broader enterprise context, identify which existing systems will interact with AI workloads, evaluate whether data quality and governance controls are sufficient to support responsible AI use, and ensure AI investments align with existing modernization priorities rather than creating fragmented technology landscapes. This foundation supports the ongoing AI inventories and risk assessments required under OMB M-25-21 guidance.
Why is a purpose-built application portfolio management (APM) platform needed instead of spreadsheets or general-purpose tools?
Spreadsheet-based approaches typically fail because they cannot maintain continuously updated application inventories, enforce governance workflows, or support repeatable assessment and decision processes at enterprise scale. Spreadsheets may capture a snapshot for a specific oversight cycle, but they cannot maintain real-time dependencies, track changes across organizational boundaries, or connect applications to business capabilities, costs, and risks. As portfolios grow and modernization accelerates, spreadsheet-based rationalization becomes unsustainable.
A purpose-built Application Portfolio Management (APM) platform such as Bizzdesign Alfabet centralizes portfolio data, integrates with existing systems (financial databases, CMDBs, cloud management platforms), automates assessments, enables collaboration across stakeholders, and converts analysis into governed portfolio actions. This allows agencies to sustain portfolio visibility as an operational discipline rather than a periodic reporting exercise.
What capabilities should agencies look for in an application portfolio management (APM) platform?
Agencies evaluating Application Portfolio Management (APM) platforms should prioritize capabilities that support continuous portfolio visibility, repeatable governance processes, and integration with existing enterprise systems. Essential capabilities include:
- A centralized application repository serving as the authoritative source of portfolio information.
- Continuous data synchronization with existing systems (CMDBs, asset inventories, financial systems).
- Workflow-based questionnaires with ownership assignment and validation controls.
- Role-based access ensuring application owners can update systems they manage while maintaining governance.
- Built-in analytics and dependency visualization for multidimensional portfolio analysis.
- Integrated financial views mapping costs to applications, services, and business capabilities.
- Centralized scoring logic ensuring consistent evaluation criteria across departments.
- Portfolio evaluation frameworks (e.g., TIME: Tolerate, Invest, Migrate, Eliminate).
- Program portfolio management linking application portfolio decisions to funded initiatives.
Additionally, FedRAMP authorization is a foundational requirement for US government agencies.
Bizzdesign Alfabet addresses these requirements. It also offers a preconfigured alignment to the CIO Council Application Rationalization Playbook, out-of-the-box integrations with ServiceNow and other enterprise systems, and a centralized repository that connects applications to mission services, costs, risks, and dependencies.
How can agencies establish continuous application portfolio visibility?
Establishing continuous portfolio visibility requires shifting from episodic inventory exercises to sustained governance practices supported by the right platform, processes, and organizational commitment.
Agencies should begin by designating an authoritative system of record for application portfolio data. This centralized repository becomes the foundation for all portfolio decisions and governance activities. Next, agencies must establish integration pathways that enable continuous data synchronization between the portfolio repository and existing systems such as financial databases, CMDBs, cloud management platforms, and procurement systems. These integrations eliminate the need for manual reconciliation and ensure portfolio data remains current without requiring teams to reconstruct inventories for each oversight cycle.
Governance policies must reinforce the practice operationally. Agencies should align assessment frameworks to recognized methodologies such as the Federal CIO Council Application Rationalization Playbook, which provides standardized evaluation criteria and repeatable processes.
Finally, agencies must build cross-functional participation across business owners, technical teams, security personnel, and financial stakeholders. Purpose-built APM platforms such as Bizzdesign Alfabet enable this collaboration by providing role-based access, standardized workflows, and enterprise-wide dashboards that make portfolio data accessible across organizational boundaries.
Why is FedRAMP authorization important for application portfolio management (APM) platforms in government?
FedRAMP (Federal Risk and Authorization Management Program) provides standardized security assessment, authorization, and continuous monitoring for cloud service providers. OMB policy requires federal agencies to use FedRAMP-authorized cloud services when deploying cloud solutions that process federal data.
For agencies adopting cloud-based Application Portfolio Management (APM) platforms, FedRAMP authorization ensures that these platforms meet federal security requirements based on NIST standards and FISMA-aligned controls, supporting the secure handling of sensitive portfolio data (including sensitive information about system architectures, costs, dependencies, and vulnerabilities).It also provides value to agencies in reducing the required workload and shortening the timeline for achieving ATO (Authority to Operate) through inherited security controls.
How does Bizzdesign Alfabet support application rationalization?
Bizzdesign Alfabet is an Application Portfolio Management (APM) that operationalizes the CIO Council Playbook through the Application Rationalization Accelerator for U.S. Government, a preconfigured solution aligned to the Playbook's six-step methodology.
The Accelerator enables agencies to initiate structured portfolio analysis shortly after implementation by providing standardized assessment attributes, scoring logic, and reporting structures. Out-of-the-box integrations with ServiceNow (CMDB), Flexera ITpedia (technology catalogue), and enterprise architecture repositories enable continuous data synchronization without custom development.
Unlike spreadsheets or operational tools, Bizzdesign Alfabet connects applications to mission services, costs, risks, and dependencies within a centralized repository. This allows agencies to sustain rationalization as an ongoing discipline, respond to oversight requirements without rebuilding the portfolio baseline, and extend the same foundation into technology portfolio management, strategic portfolio management, and AI governance.
Table of contents

Maintain Visibility. Strengthen Governance. Deliver Mission Value.
Govern your application portfolio to control costs, strengthen cybersecurity, and scale AI adoption responsibly.


